(! always check domain name history)
read more (checkpoint)
Recently, Check Point engines detected a new phishing campaign impersonating the Royal Bank of Canada (RBC).
The attack starts by sending legitimate-looking e-mails containing a PDF attachment to multiple organizations and victims from Canada.
Connecting the Dots
The phishing website which appeared in the PDF attachments we investigated at first (royalexpressprofile[.]com) resolved to a Ukrainian IP address: 176.119.1[.]80.
Examining this IP address revealed that it hosted more domains impersonating RBC in addition to other banks:
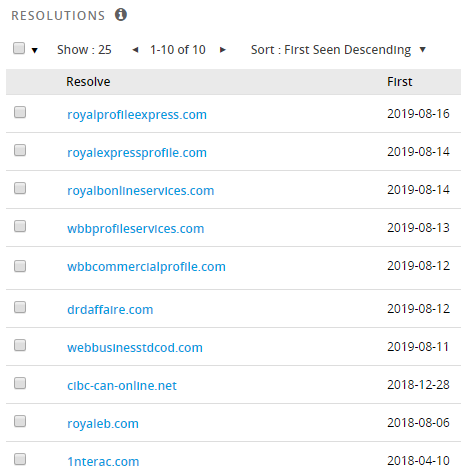
Figure 8: Domains resolving to 176.119.1[.]80
As it turns out, there were many more IP addresses on the same netblock 176.119.1[.]0/24 that were part of a massive infrastructure used to launch phishing attacks that attempt to steal banking credentials from Canadian victims:
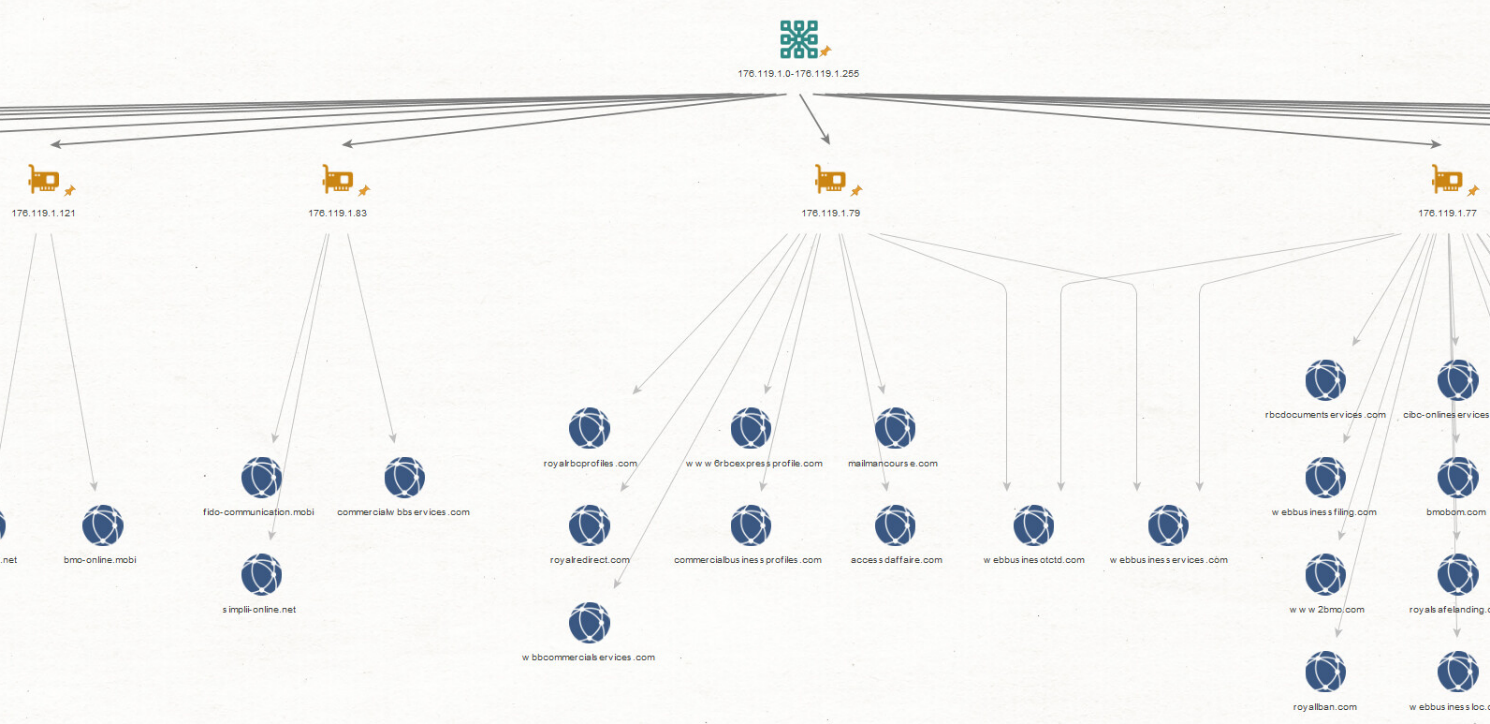
Figure 9: Phishing websites resolving to IPs on the same netblock
read more (checkpoint)
read more (checkpoint)
Recently, Check Point engines detected a new phishing campaign impersonating the Royal Bank of Canada (RBC).
The attack starts by sending legitimate-looking e-mails containing a PDF attachment to multiple organizations and victims from Canada.
Connecting the Dots
The phishing website which appeared in the PDF attachments we investigated at first (royalexpressprofile[.]com) resolved to a Ukrainian IP address: 176.119.1[.]80.
Examining this IP address revealed that it hosted more domains impersonating RBC in addition to other banks:
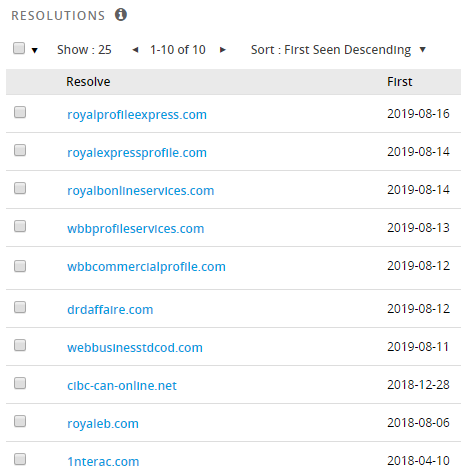
Figure 8: Domains resolving to 176.119.1[.]80
As it turns out, there were many more IP addresses on the same netblock 176.119.1[.]0/24 that were part of a massive infrastructure used to launch phishing attacks that attempt to steal banking credentials from Canadian victims:
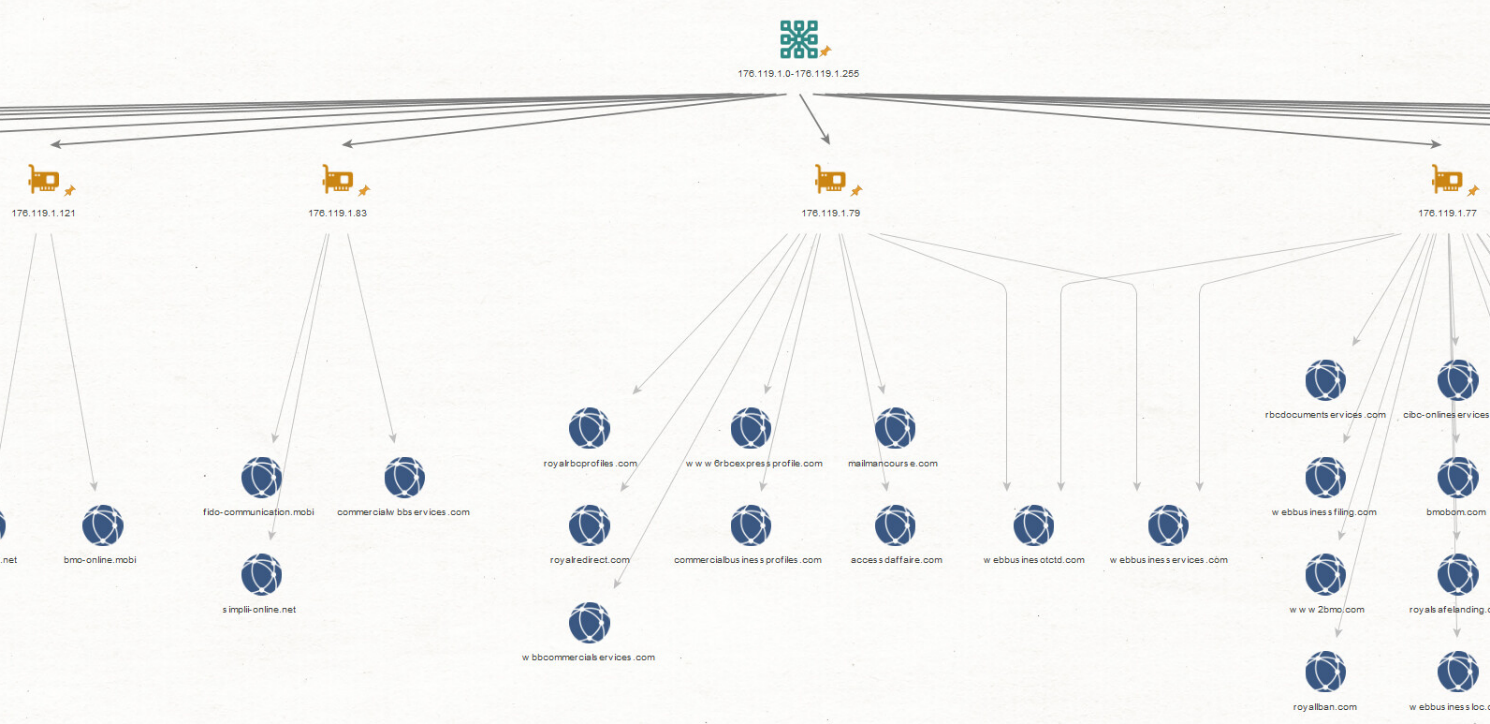
Figure 9: Phishing websites resolving to IPs on the same netblock
read more (checkpoint)







